Secure control of wireless networked control systems subject to stochastic deception attacks

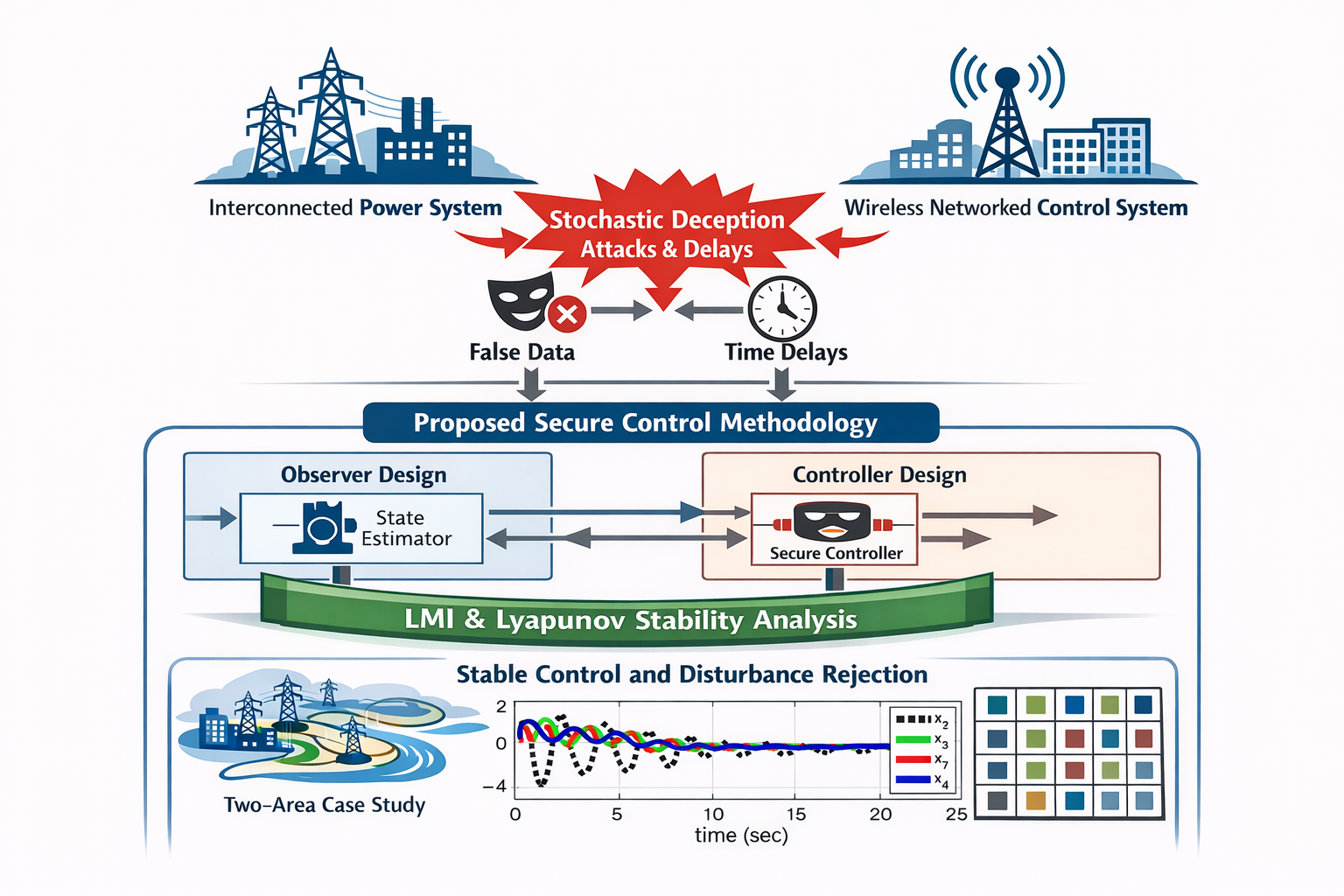
Given that power systems are essential to modern life and electricity demand continues to rise, ensuring their reliable and secure operation has become a critical priority. Wireless networked control systems (WNCSs), which rely on wireless channels for communication between controllers, sensors, and actuators, are increasingly deployed in energy systems such as multi-area interconnected power systems to enhance flexibility and scalability. WNCSs are susceptible to deception attacks and time-varying communication delays that can compromise interconnection stability and deteriorate performance. This paper presents an observer-based secure control methodology that models deception via independent Bernoulli processes with unknown attack probabilities, while explicitly considering actuation and measurement delays. Using a Lyapunov stability framework, we established computationally feasible linear matrix inequality conditions enabling the co-design of the controller and observer with proven stability and disturbance rejection. A two-area interconnected power system case study validates the approach. The proposed method was tested with offline gains covering nine scenarios. Results indicate that the method sustains closed-loop performance across all nine combined attack/delay scenarios and recovers quickly even in worst-case conditions, supporting secure control of WNCSs in realistic adversarial environments.
- Aljubouri MA, Iskandarani MZ. Comparative analysis of coding schemes for effective wireless communication. Indones J Electr Eng Comput Sci. 2024;34(2):926–940. https://doi.org/10.11591/ijeecs.v34.i2.pp926-940
- Qasem N. Measurement and simulation for improving indoor wireless communication system performance at 2.4 ghz by modifying the environment. IEEE Access. https://doi.org/10.1109/ACCESS.2024.3426490
- Hamdan MM, Mahmoud MM. Analysis and challenges in wireless networked control system: A survey. Int J Robot Control Syst. 2022;2(3):492–522. https://doi.org/10.31763/ijrcs.v2i3.731
- Park P, Ergen SC, Fischione C, Lu C, Johans- son KH. Wireless network design for control systems: A survey. IEEE Commun Surv Tutor. 2017;20(2):978–1013. https://doi.org/10.1109/COMST.2017.2780114
- Bello O, Zeadally S. Intelligent device-to-device communication in the internet of things. IEEE Syst J. 2014;10(3):1172–1182. https://doi.org/10.1109/JSYST.2014.2298837
- Lu X, Li J. Improving stability and performance in iot-driven networked control systems. Comput Electr Eng. 2024;119:109537. https://doi.org/10.1016/j.compeleceng.2024.109537
- Aslam MM, Li W, Liu W, Qi Y, Saleem U, Riaz S. A review of integrated modeling and simulation of control and communication systems in smart grid. Comput Electr Eng. 2024;119:109553. https://doi.org/10.1016/j.compeleceng.2024.109553
- Al-Dabbagh AW. Design of a wireless control system with unreliable nodes and communication links. IEEE Trans Cybern. 2017;49(1):315–327. https://doi.org/10.1109/TCYB.2017.2772869.25
- Majid M, Habib S, Javed AR, Rizwan M, Srivastava G, Gadekallu TR, Lin JC-W. Applications of wireless sensor networks and internet of things frameworks in the industry revolution 4.0: A systematic literature review. 2022;22(6):2087. https://doi.org/10.3390/s22062087
- Wang Y, Wu S, Lei C, Jiao J, Zhang Q. A review on wireless networked control system: The communication perspective. IEEE Internet Things J. https://doi.org/10.1109/JIOT.2023.3342032
- Ma Y, Guo J, Wang Y, Chakrabarty A, Ahn H, Orlik P, Guan X, Lu C. Optimal dynamic transmission scheduling for wireless networked control systems. IEEE Trans Control Syst Technol. 2022;30(6):2360–2376. https://doi.org/10.1109/TCST.2022.3141581
- Alzubi OA. A deep learning-based frechet and dirichlet model for intrusion detection in iwsn. J Intell Fuzzy Syst. 2022;42(2):873–883. https://doi.org/10.3233/JIFS-189756
- Alzubi OA, Alzubi JA, Alazab M, Alrabea A, Awajan A, Qiqieh I. Optimized machine learning-based intrusion detection system for fog and edge computing environment. 2022;11(19):3007. https://doi.org/10.3390/electronics11193007
- Yuan Y, Yuan H, Ho DW, Guo L. Resilient control of wireless networked control system under denial-of-service attacks: A cross-layer design approach. IEEE Trans Cybern. 2018;50(1):48–60. https://doi.org/10.1109/TCYB.2018.2863689
- Liu Z, Li Y, Li L, Ma K, Yang Y. On the security and stability for wireless networked control systems with external attack and disturbances. Int J Robust Nonlinear Control. https://doi.org/10.1002/rnc.6260
- Cetinkaya A, Ishii H, Hayakawa T. Effects of jamming attacks on wireless networked control systems under disturbance. IEEE Trans Autom Control. 2022;68(2):1223–1230. https://doi.org/10.1109/TAC.2022.3153275
- Alyazidi NM, Mahmoud MS. L1 adaptive net- worked controller for islanded distributed generation systems in a microgrid. Int J Syst Sci. 2018;49(12):2507–2524. https://doi.org/10.1080/00207721.2018.1487093
- Al-Yazidi NM, Al-Wajih YA, Mahmoud MS. Iterative learning control for load frequency in cyber-attacked multi-area power systems. IEEE Access. https://doi.org/10.1109/ACCESS.2023.3309150.26
- Xu Z, Yang X, Li X, Lu J. Input-to-state stability of switched network control systems under unknown deception attacks. IEEE Trans Cybern https://doi.org/10.1109/TCYB.2024.3376695
- Shi H, Zhang Y. hinfty control for networked control systems with packet loss and deception attack. in: 2024 39th Youth Academic Annual Conference of Chinese Association of Automation (YAC), IEEE, 2024, pp. 579–584. https://doi.org/10.1109/YAC63405.2024.10598802
- Devanathan B, Selvaraj P, Suyampulingam A. Finite-time control for iot-enabled microgrids using distributed state estimation under deception attack. in: 2024 IEEE 21st India Council Inter- national Conference (INDICON), 2024, pp. 1–5. https://doi.org/10.1109/INDICON63790.2024.10958434
- Li F, Li K, Peng C, Gao L. Dynamic event- triggered fuzzy control of dc microgrids under fdi attacks and imperfect premise matching. Int J Electr Power Energy Syst. 2023;147:108890. https://doi.org/10.1016/j.ijepes.2022.108890
- Li F, Li K, Peng C, Gao L. Dynamic event- triggered fuzzy non-fragile control of dc micro- grids. ISA Trans. 2023;142:83–97. https://doi.org/10.1016/j.isatra.2023.07.012
- Meng Q, Kasis A, Yang H, Polycarpou MM. Secure state estimation of networked switched systems under denial-of-service attacks. Eur J Control. 2024:101037. https://doi.org/10.1016/j.ejcon.2024.101037
- Abdelkader S, Amissah J, Kinga S, Mugerwa G, Emmanuel E, Mansour D-EA, Bajaj M, Blazek V, Prokop L. Securing modern power systems: Implementing comprehensive strategies to enhance resilience and reliability against cyber- attacks. Results Eng. 2024:102647. https://doi.org/10.1016/j.rineng.2024.102647
- Huang Y, Huang L, Zhu Q. Reinforcement learning for feedback-enabled cyber resilience. Annu Rev Control. 2022;53:273–295. https://doi.org/10.1016/j.arcontrol.2022.01.001
- Ding D, Wang Z, Q.-Han L, Wei G. Security control for discrete-time stochastic nonlinear systems subject to deception attacks. IEEE Trans Syst Man Cybern Syst. 2016;48(5):779–789. https://doi.org/10.1109/TSMC.2016.2616544
- Hamdan MM, Mahmoud MS, Baroudi UA. Event-triggering control scheme for discrete time cyberphysical systems in the presence of simultaneous hybrid stochastic attacks. ISA Trans. 2022;122:1–12. https://doi.org/10.1016/j.isatra.2021.04.027.27
- Mahmoud M, Selim S, Shi P, Baig M. New results on networked control systems with non- stationary packet dropouts. IET Control Theory Appl. 2012;6(15):2442–2452. https://doi.org/10.1049/iet-cta.2012.0487
- Mahmoud MS, Khalid HM, Hamdan MM. Cyberphysical infrastructures in power systems: architectures and vulnerabilities.. Academic Press, 2021.https://doi.org/10.31763/ijrcs.v2i3.731

